Last semester I took my first computer science class. We covered everything from open source software to government censorship. However, what I found to be the most interesting topic was computer hacking. Our class discussed the numerous reasons behind computer hacking, but one reason in particular stood out from all the rest… using computer hacking as a threat against people’s health. If you are at all like me, right about now  you’re probably thinking how in the world can computer hacking be linked to health policy? The answer is through medical device security.
you’re probably thinking how in the world can computer hacking be linked to health policy? The answer is through medical device security.
Implantable medical devices, such as pacemakers and implantable cardioverter-defibrillator (ICD), are run from software. Basically these small medical devices are like miniature computers in your body helping to ensure that your internal bodily functions occur properly. Since these small devices use software to function, they are susceptible to computer hacking just like the computer you’re using to read this article right now.
So, what exactly can a computer hacker see and do once he/she has hacked into a medical device? The hacker can view the medical record of the patient, the diagnosis, and even the implanting physician. However, what’s more frightening is that if the computer hacker hacked into an ICD, he/she can actually send a wireless fatal shock to the patient. During the implantation of ICDs the doctors must test the device in order to make sure it is working properly. They send a signal to the ICD that induces a fatal heart rhythm so they can be sure that the ICD successfully remedies the issue. Basically they send a fatal shock to the patient’s heart in order to make sure the ICD can do its job correctly. With the appropriate knowledge, someone can actually disable all the therapies programmed on the device and then send the command to induce the fatal heart rhythm.
Now you’re probably slightly dumbfounded. You’re not alone. I remember hearing this information for the first time in class and actually having a hard time believing it at first. Seems like science fiction right? However, the 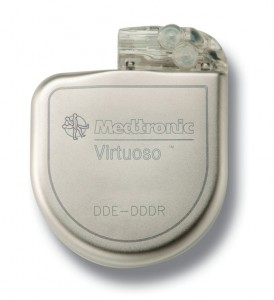 truth is that as technology advances, healthcare and computers are becoming more and more integrated. Each year 135,000 patients receive new ICDs. In 2005 the FDA issued a guidance report concerning cyber security and medical devices. This guidance does not establish “legally enforceable responsibilities.” Experts recognize the real possibility of software hacking when it comes to medical devices, but most argue that the actual threat of malicious behavior is very low. Most claim that little to no data has shown medical device hacking in the past.
truth is that as technology advances, healthcare and computers are becoming more and more integrated. Each year 135,000 patients receive new ICDs. In 2005 the FDA issued a guidance report concerning cyber security and medical devices. This guidance does not establish “legally enforceable responsibilities.” Experts recognize the real possibility of software hacking when it comes to medical devices, but most argue that the actual threat of malicious behavior is very low. Most claim that little to no data has shown medical device hacking in the past.
Personally, the lack of regulatory measures in place is disturbing to me. Regardless of past events, the threat of medical devices being hacked and posing serious threats to people’s lives is a situation that should be acted on now. If society recognizes the plausibility of medical devices becoming hacked, why wait for a catastrophe to make regulatory changes?
As technology and healthcare become more intermingled this issue will only grow. Pacemakers and ICDs are not the only devices that rely on computers and the Internet. Insulin pumps are also vulnerable to computer hackers, and medical records are stored through computer systems and large databases. While our advancements in medicine are fantastic, we need to be wary of some possible implications that can arise from blurring the line between medicine and technology.
I personally believe that the FDA should replace their guidance report with strict regulatory policy that addresses medical device security. Security measures should be legally enforced. Technology often moves faster than policy, and policies are constantly forming in response to new technological advancements. These new technological advancements in the healthcare industry, however, are not dealing with copyrighted music; they are dealing with people’s lives. Therefore, as a society, we must try to stay ahead of the curve and take proactive steps in combatting cyber threats rather than reactive steps. The FDA should constantly update their regulations in order to meet the latest security demands.
I think that many people are reluctant to take this issue seriously because it seems so outlandish and futuristic, but the truth is that it is a very real concern. Like most, I have a computer program installed on my personal computer to protect me against viruses and other threats. Why should we not take the same precautions when the computer is controlling our own bodily functions?



1 pings